Training course: Soffid for IAM professionals 2. Policies
Introduction
In this chapter we are going to learn Soffid’s different authentication policies and what differentiates each one from the others. We will also learn how to extend the data model with metadata, creating user objects, and how to change configuration parameters in the Global Settings section. Finally, we will introduce the Attribute translation variables and how to use them, as well as what difference there is between Soffid Connectors and Add-ons.
Product | Soffid IAM |
Goal | To know policies, user objects, change the configuration, and what
add-ons and connectors are. |
Profile | Identity Management Professionals |
Prerequisites | Knowledge of any Identity Management tool |
Level | Medium |
Duration | 00:30 |
Unidades |
|
| Responsable | Joan Calabria |
|---|---|
| Última actualización | 13/05/2026 |
| Tiempo de finalización | 1 hora 33 minutos |
| Miembros | 1 |

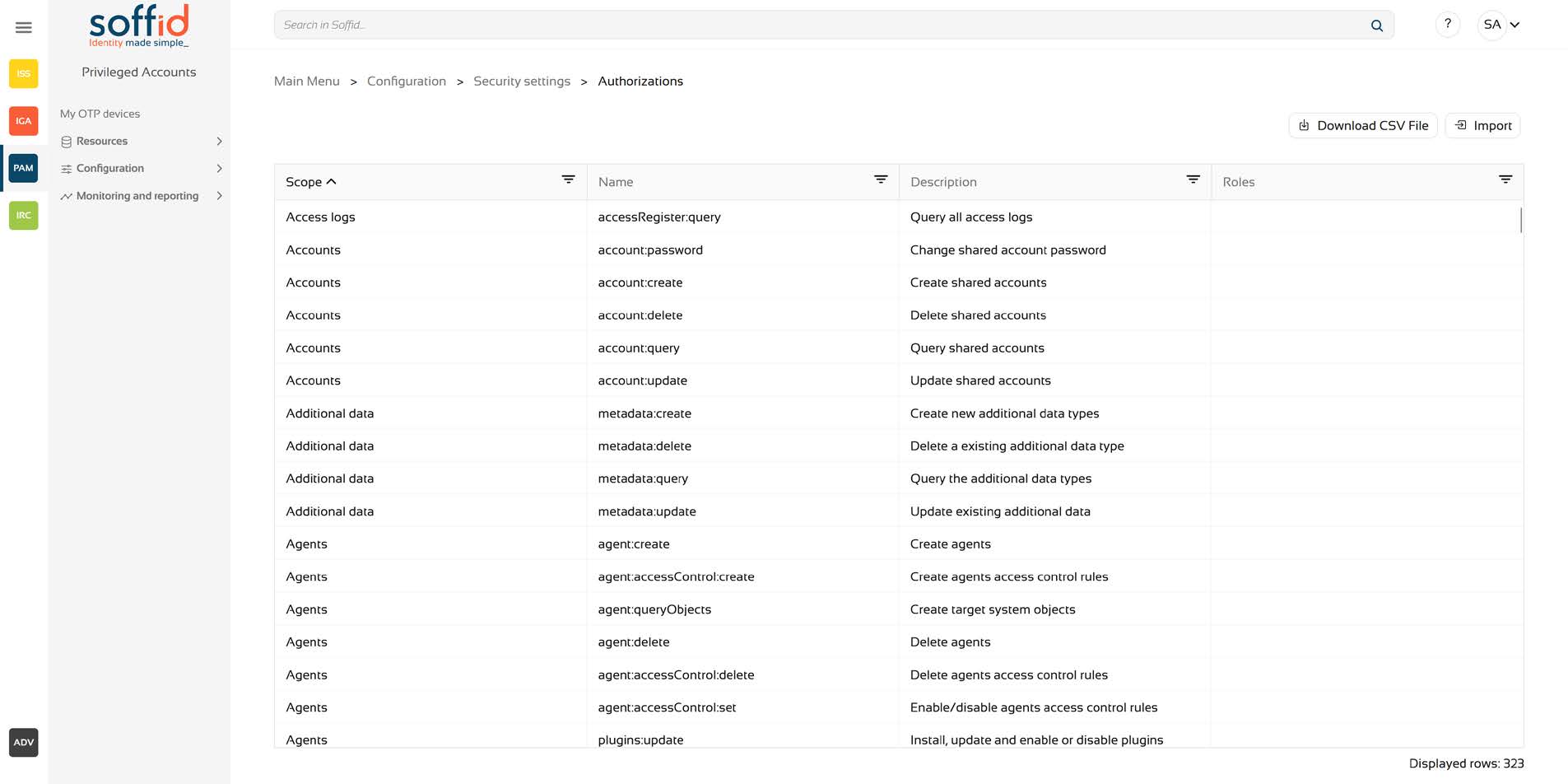
1.1 Authentication Policies
We'll start with the authentication section because it defines how users will authenticate when accessing the console. Basically, two types of authentication are accepted: username and password, and an external identity provider, which can be Soffid's own identity provider. We can enable them independently.

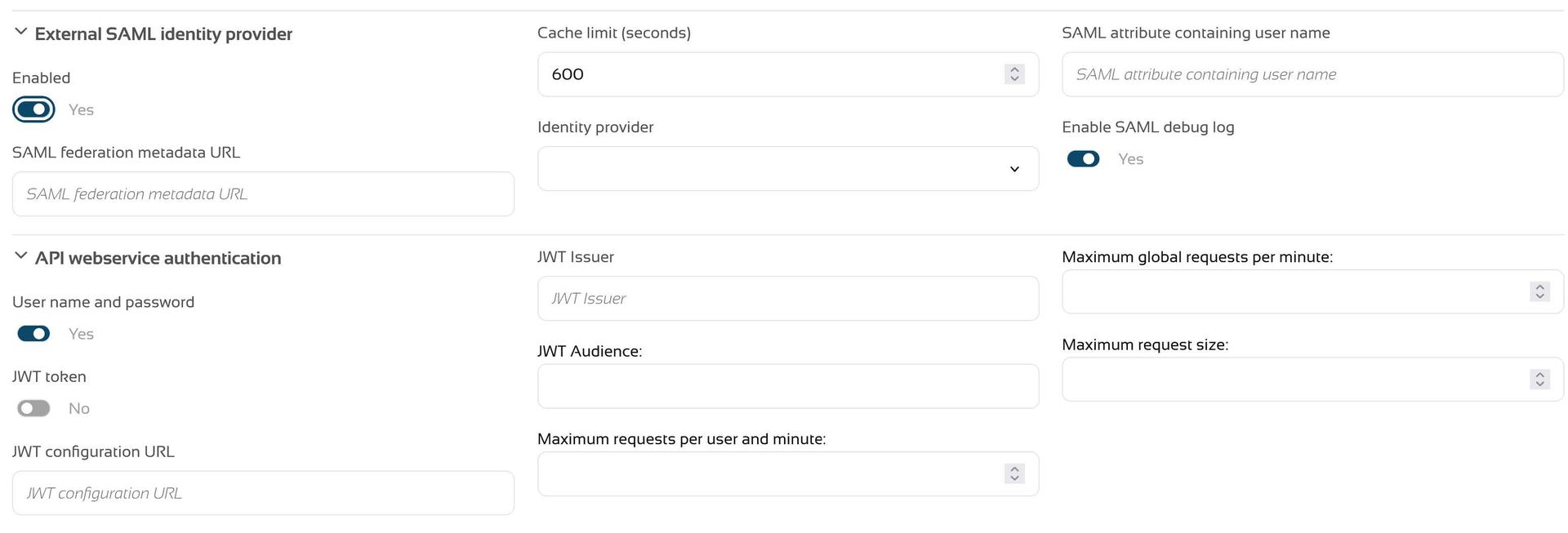
This setting will change the default behavior of the login screen. For example, as configured in the image above, it allows me to log in in two ways: with a username and password or with an external identity provider. If the external provider is disabled, that option disappears. And disabling the username and password option will automatically trigger authentication against the Identity Provider.
Aside from this, authentication with a username and password can be strictly local or accept passwords from trusted agents. This is done using the Forward authentication request to trusted target systems.
- tokens JWT
- user & password
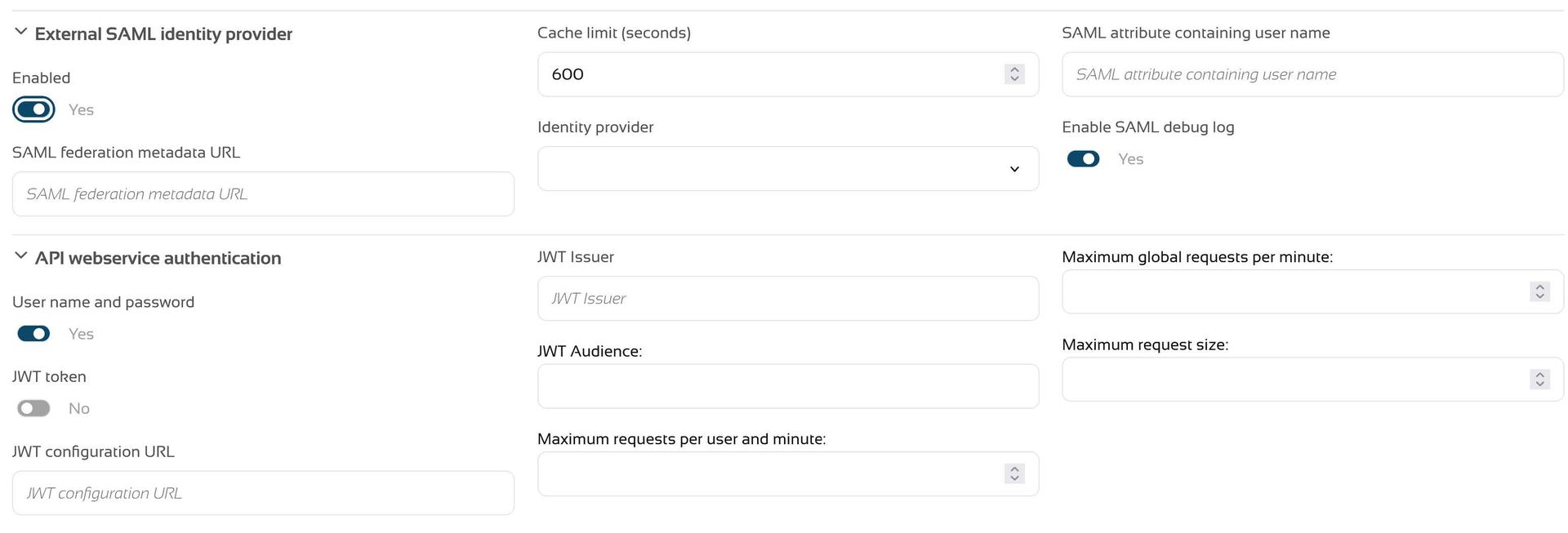
In the case of SAML, what we configure is the SAML metadata URL and, if we use a JWT token, the JWT configuration for the web services is placed in the corresponding box, indicating the Issuer, Audience, etc.
In the Second Factor Authentication configuration section, you can enable additional authentication when accessing certain screens. Regular expressions can be used in this field and it activates an additional authentication, after the initial authentication.
INTRODUCTION
Ver todo
In this chapter we are going to learn Soffid’s different authentication policies and what differentiates each one from the others. We will also learn how to extend the data model with metadata, creating user objects, and how to change configuration parameters in the Global Settings section. Finally, we will introduce the Attribute translation variables and how to use them, as well as what difference there is between Soffid Connectors and Add-ons.
CHAPTER 1: System Architecture
Ver todo
We'll start with the authentication section because it defines how users will authenticate when accessing the console. Basically, two types of authentication are accepted: username and password, and an external identity provider, which can be Soffid's own identity provider. We can enable them independently.

This setting will change the default behavior of the login screen. For example, as configured in the image above, it allows me to log in in two ways: with a username and password or with an external identity provider. If the external provider is disabled, that option disappears. And disabling the username and password option will automatically trigger authentication against the Identity Provider.
Aside from this, authentication with a username and password can be strictly local or accept passwords from trusted agents. This is done using the Forward authentication request to trusted target systems.
- tokens JWT
- user & password
In the case of SAML, what we configure is the SAML metadata URL and, if we use a JWT token, the JWT configuration for the web services is placed in the corresponding box, indicating the Issuer, Audience, etc.
In the Second Factor Authentication configuration section, you can enable additional authentication when accessing certain screens. Regular expressions can be used in this field and it activates an additional authentication, after the initial authentication.

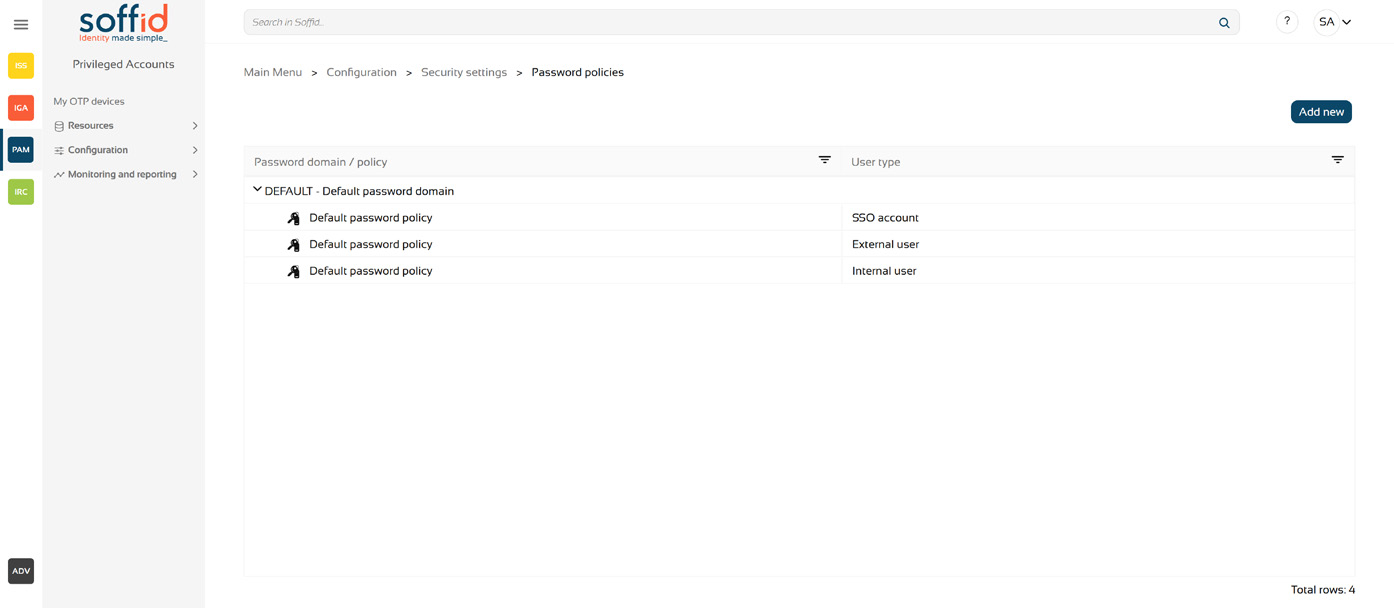
In Password policies we can define multiple password policies for different types of users and agent types. In the image we can see some default configuration, consisting of policies for External users, Internal users,Secured accounts and SSO accounts.
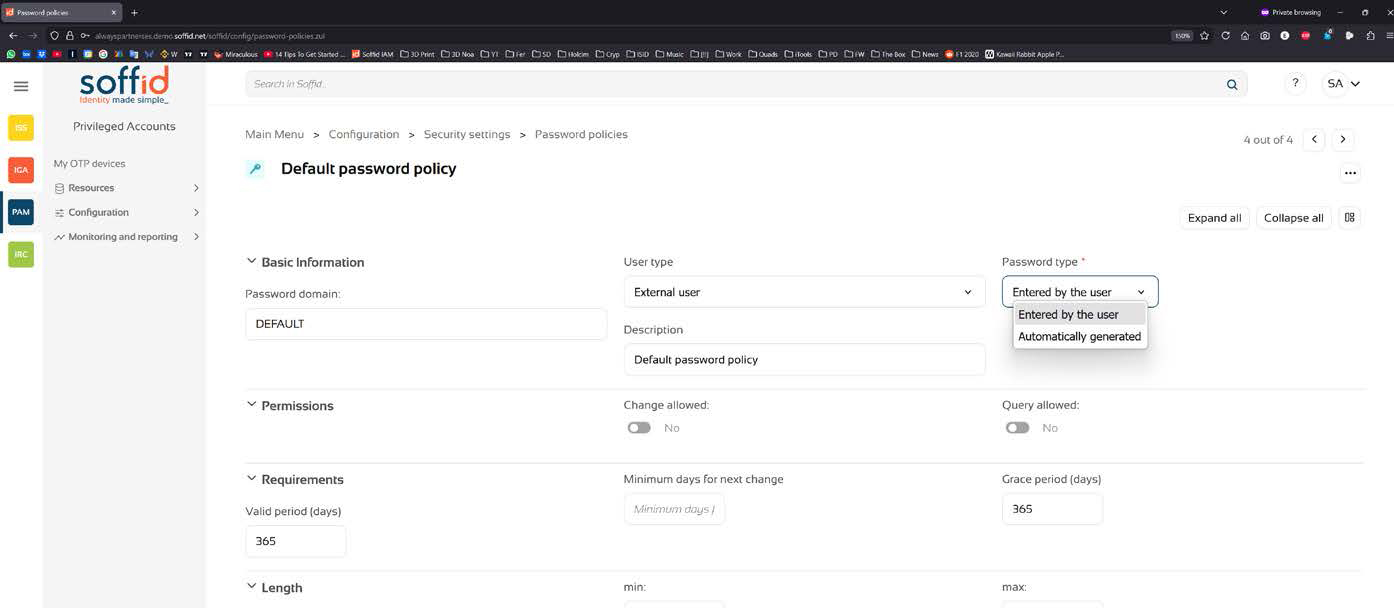
For each option you can define the User type and the Password type. In Permission you can control to allow the password change or query by the user, as well as the password Complexity and Validation rules which allows to specify forbidden words, that cannot be used as part of a password.
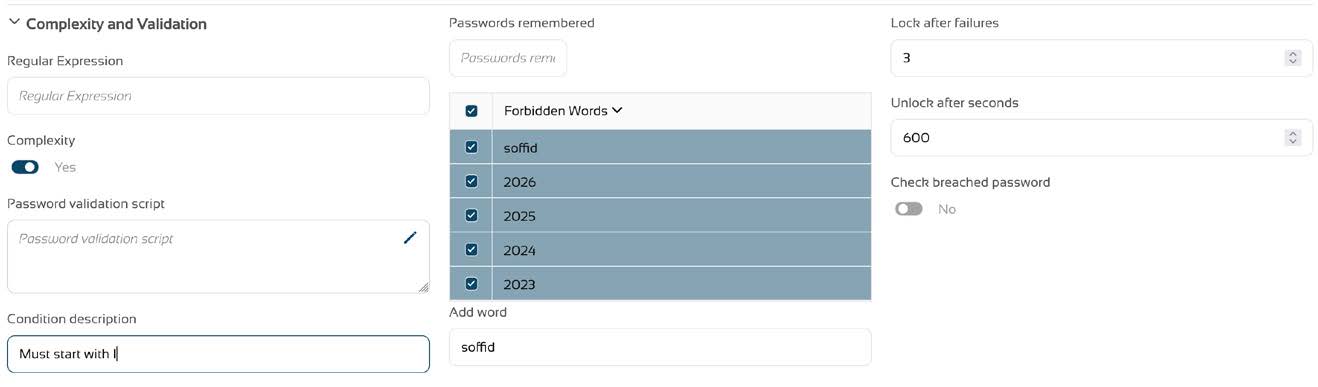
There is also the possibility to define a Password validation script that can do more complex checks on user entered passwords to make them conform to strict security standards.
All changes applied to password policies, will apply only to new passwords from that moment on, and not to already existing passwords.